In computer networking and telecommunications, when a transmission unit is sent from the source to the destination, it contains both a header and the actual data to be transmitted. This actual data is called the payload. The header contains the protocol information as well as the source and destination addresses, which are required for delivery of the payload. The payload is required by the destination client.
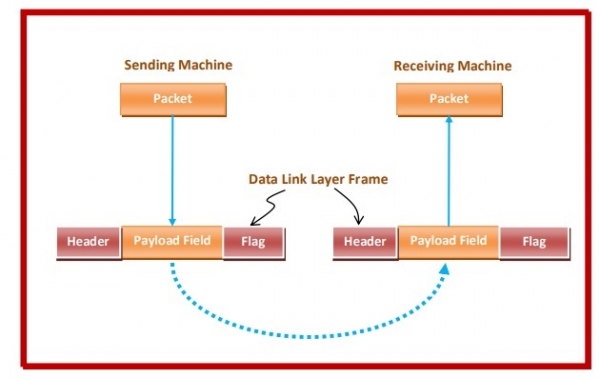
The following diagram depicts encapsulation of payload field in a data link layer frame. The data packet from the upper layer is framed by adding a header that contains the control information for data transmission, the payload field containing the actual data and the end flag that marks the end of the data frame.
Fixed and Variable Payload
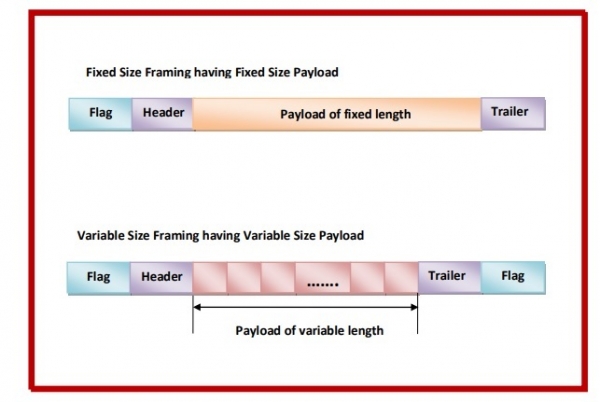
The payload field may be of fixed size or of variable size. If the payload field is of fixed size, then the frame becomes of fixed size. Fixed size frames do not need any end flag, since the frame length acts as delimiter of the frame. In case of variable length payload, a pattern is used as a delimiter to determine the size of frame. Alternatively, a length field is kept that contains the frame size.
Comments
Post a Comment